The title says it all.
advertising / internet / social media / social networks
Posted on:
Trying To Escape The Cycle Of Enshittification
As this current wave of people have been leaving the rampant fascism actively being pushed by Musk on X, many people have ended up on Bluesky. I’ve also […]
games / internet / roleplaying games / self-promotion
Posted on:
Game And Give: Make A Donation, Get In My D&D Games For Free
Gaming! Raising money for good folks! At the same time!
advertising / business / computers / internet / online / relationships
Posted on:
I Was Invited To And Kicked Off Match.Com Within 15 Minutes
This is a story about bad advertising, bad UI design, and bad customer service.
communication / internet / online / social media
Posted on:
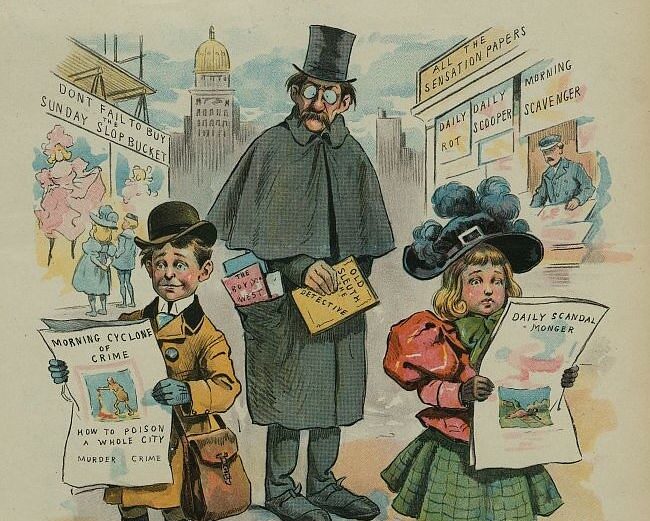
Even Trolls Have More Courage
If you’re brave enough to stir the pot, then you should be brave enough to admit when you’re wrong.
computers / internet / privacy / social media
Posted on:
Facebook Is Removing Posts About Its AI Scraping Policies
Meta doesn’t want you to know what they’re doing with your data — or how to opt out.