 We often worry about our safety and privacy online – including that of our children. (If you haven’t read it before, my Practical Privacy Online guide still holds a lot of good info.) But we don’t think about their phones.
We often worry about our safety and privacy online – including that of our children. (If you haven’t read it before, my Practical Privacy Online guide still holds a lot of good info.) But we don’t think about their phones.
Sure, there’s the problem that tools like K9 Web Protection don’t work with smartphones (though I believe there’s some ways to get similar functionality), but your kid (or you!) doesn’t have to have a smartphone in order to severely compromise your security.
The background: My son had gotten several text messages from a number he didn’t recognize. He started chatting with the person, and by the time his mother found out, he’d given away more personal information than she was comfortable with. This particular instance turned out to be a prank from some “friends” of a friend, but none of us knew it at the time. For all we knew, it was an instance of wardialing … and while you can’t (always) get a name for a cell phone number, you can usually get the general location, such as the city and state.
I was concerned about social engineering – that is, the practice of getting someone to give up secure or confidential information willingly. While I don’t have any real practice in that – though I’ve seen it described – I do have a tiny bit of experience doing cold readings. Cold reading is the technique that con artists posing as psychics and mediums use.
I was at a different location, and realized that he didn’t have my Google Voice number in his address book. Surely, after his mom had just berated him for this security violation, he wouldn’t do the same damn thing again, right?
My notes in this transcript are in italics. Some data is obfuscated, of course. “Me” is me, and “Kiddo” is him. He’s 13. The time/date stamp is right after each line, so you can see how far I got in an hour of texting. I tried to pretend (to myself) that I didn’t know who was on the other side of the conversation.
 Me: Hey u there? 8:34 PM
Me: Hey u there? 8:34 PM
Kiddo: Is this zach 8:38 PM
Me: Got ur $ I owe u 8:41 PM
Me: From aug 8:42 PM
I figured that one of two things was true here – the person had either lent money, or would gladly accept someone wanting to “pay them back” for money they hadn’t lent. Con artists use this technique all the time, letting the mark doom themselves through their own greed.
Me: Had 2 get new phone 8:44 PM
Me: Lost all my #s. 🙁 8:44 PM
Kiddo: Who is this 8:45 PM
Me: Wait did I get wrong #? 8:46 PM
Me: Had all written down. Who r u? 8:46 PM
Me: Maybe I got mixed up w names and #s 8:47 PM
Kiddo: Chris 8:47 PM
I took a “guess” here that Chris was a boy, so I used a girl’s name back. Lindsey is the name of an acquaintance who had given my workmates and I cupcakes earlier that day. It’s also a fairly common name – but not THAT common. I could also – in a pinch – try to pass it off as a male name.
Me: Which chris? This is lindsey. 8:48 PM
Me: I know 2 many chris! 🙂 8:48 PM
Kiddo: What is your name 8:48 PM
Me: Lindsey! 8:49 PM
Me: U don’t remember me? 🙁 8:49 PM
Kiddo: Ya i do 8:49 PM
Because who admits not remembering someone who remembers you? Also, by this point it’s pretty clear I’m dealing with a kid/teen.
Me: Which chris? 8:50 PM
Kiddo: The one u txt earlyer who was confused about who u were. How did u get my number 8:52 PM
Me: Ur friend, remember? I got the $ I owe u but don’t remember which place is u? 8:53 PM
Kiddo: Which friend tell me their name 8:54 PM
Me: I don’t remember I thought u were cute 8:55 PM
I almost thought he had me here. This was the only dodge I could think of to avoid guessing a friend’s name – because while he probably knew a “Lindsey” (something I really didn’t know) – I don’t want the story to get too complicated or involving more people. So I played on the other thing that tends to get people… “I thought you were cute.”
Me: U gave me $ for pop 8:56 PM
Me: So can I give u ur $ now? 8:59 PM
Me: I’m near ur house but need to know which 1 9:00 PM
Me: & I wanna c u again 9:02 PM
Me: So can I c u? 9:02 PM
Plausible reason to get his address… if he gave it to me right away, I’d have to say something came up and I’d come back later…
Kiddo: Ohhhhhhh. From the [CITYNAME] wreck center at the pool 9:04 PM
Me: Yeah silly 9:04 PM
Me: So? 9:06 PM
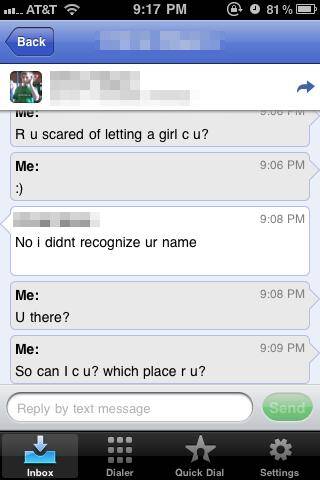
Me: R u scared of letting a girl c u? 9:06 PM
Classic technique here among con artists (and pickup artists, who essentially do the same thing). Flatter, then “neg” – as in “put down”. I saw a 419 scammer try to do this to a professional during one of my grad school classes.
Me: 🙂 9:06 PM
Kiddo: No i didnt recognize ur name 9:08 PM
Me: U there? 9:08 PM
Me: So can I c u? which place r u? 9:09 PM
Me: Cmon I gotta go home soon 9:13 PM
More “neg”
Me: Do u wnt 2 c me? 9:14 PM
Me: Yes I said u were cute! 9:18 PM
More flattery.
Kiddo: Yes sorry. My building num. Is XXXXXXXX door letter XXXX. But not tonight tomorow maybe 9:20 PM
Match, game, set. At this point, I called him from my GVoice number (after texting him that “On the internet, nobody knows you’re a dog”) and told him what I had done. I pointed out that I could have easily found out when he wasn’t there at this point and broken in… or found out when he was home alone, and worse stuff happen. And I pointed out that I had no idea who Lindsey was, and that I’d guessed at everything. We went back through the chat log and discussed how he volunteered practically all the information except for some vague good guesses on my part.
It was frighteningly easy to do this. If you think your kids (or you) are too smart to fall for this, you are wrong. These are very specific techniques that have been in use for centuries as part of a con artist’s arsenal.
What should you do? For starters:
- Emphasize the strict, no exceptions rule: NO response to texts from numbers you don’t know.
- NEVER give out personal information to random strangers. None. Nada.
- Teach your children how to recognize a scam. Whether random texts, Nigerian scammers (yes, they exist), or home-grown con artists, you only survive by being smart, alert, and informed. Not kind, not well-intentioned… smart, alert, and informed.
Many thanks to Mary Leal, whose work with the ABS program at Wright State gave me some of the awareness and skill to pull this off. She runs the Predator Project; you can read about one of her bigger cases of identity theft here.
I’m glad to say my case turned out pretty well. Kiddo later apologized to his mother: “I’m sorry I thought you were a moron about that texting thing. Dad totally got me.”
Only would have better if he’d said pwned.
