Remember the NSA, and everyone talking about encrypting their e-mail? If you even glanced at how to do that, you probably found something like this guide and it probably mentioned GPG.
But even if you’re not interested in keeping your e-mail safe, you want to have GPG installed and to have a public/private keypair for one very simple reason.
Contracts.
I, like oh, just about everyone, send “electronically signed contracts” back and forth. Realistically, they’ve been cut-and-pasted images of my signature onto PDFs or JPGs.
But now that I’ve actually got GPG set up on my machine, I can actually sign the PDF or JPG so that it is provably from me.
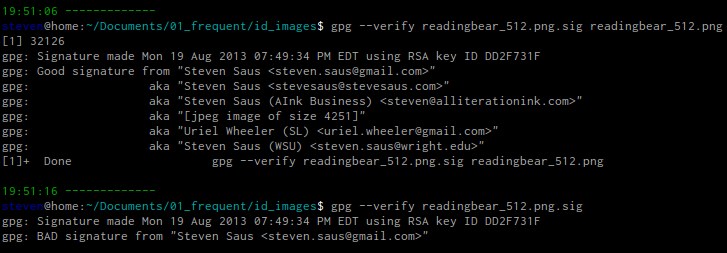
Here’s an example. I “signed” an image of my Second Life avatar reading with my private key. I’m the only one who has that.
But anyone could verify it with my public key and then when that file was altered – even just by changing the compression level slightly – the verification failed.
So that means that if the signature verifies against my public key, then you know that I actually sent the file, on purpose. Which gives us a way to actually digitally sign contracts that is already in place. Linux folks, you probably already have gpg installed on your system.
Honestly, if you follow the directions for being able to encrypt your e-mail you will have already gotten 90% of this in place. Linux folks, you have it already installed (almost certainly), and there’s nice GUIs for OSX and Windows.
Once you have GPG installed, the commandline commands to get my public key and verify any file I send to you are:
gpg –keyserver hkp://keyserver.ubuntu.com –recv-keys 0xDD2F731F
gpg –list-keys 0xDD2F731F
gpg –verify FILENAME
You can also find my public key on the MIT PGP key server.
And then when you get a signed contract from me, you’ll know what to do.
Want to sign your own document?
gpg –detach-sign file
Here are a few other cheat-sheets and howtos:
https://www.math.niu.edu/help/unix/gnupg.html
https://kb.iu.edu/data/awiu.html
[edited to include “how to sign your own document” portion. D’oh.]